Get connected. C64 OS now supports networking.
The versatile operating system for the Commodore 64,
C64 OS, brings exciting new abilities to your Wi-Fi modem.
Version 1.07 now available. From $64 CAD.
Choose bundle
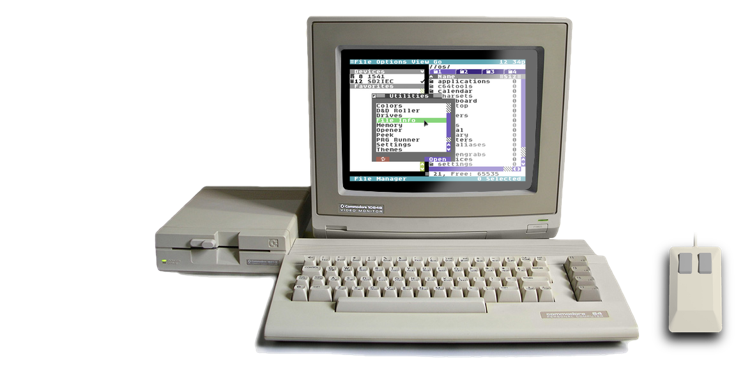
C64 OS is a modern operating system add-on that balances power and ease of use, while respecting the computer's modest specifications. C64 OS lets you do things with your Commodore 64 that Commodore would never have imagined.

Over eight years of development, C64 OS is a platform ideally suited for a whole new class of application. Applications ready to take advantage of mass storage, wireless networking, and more RAM, in an elegant, modular and expandable system, with a beautiful user experience you'll feel comfortable with from the first click.
“A match made in pure 6502 assembly language heaven.”
A licensed copy of C64 OS v1.07 includes:
- Access to the 3,500 word online Getting Started Guide
- Access to the complete 150,000 word online User's Guide
- A 50-page full-color professionally printed User's Guide Supplement
- A pre-installed copy of C64 OS v1.07 on a System Card (64 MB or 128 MB SD Card)
- An installation archive and install tools for C64 OS v1.07 for other storage media
- App Launcher, File Manager, Wikipedia, Image Viewer, C64 Archiver, 3 additional Applications and over 35 Utilities, plus 10 KERNAL modules, 20 Drivers, 26 Libraries, 28 Toolkit classes, and over 25 additional Tools
- Two high-quality promotional C64 OS vinyl stickers
- Access to ongoing patches, bug fixes and feature updates to C64 OS
- Access to new non-commercial Applications and Utilities for C64 OS
- Access to a C64 OS Discord server for support, help, bug reporting, news and community
The 64 MB System Card comes with these bonuses:
- A pre-installed CMD HD hard drive image of C64 OS v1.07 for use in VICE
- A pre-installed IDE64 hard drive image of C64 OS v1.07 for use in VICE
- A collection of C64 graphics files that can be viewed with Image Viewer
- A collection of popular HVSC SID tunes that have been relocated for use in C64 OS
The 128 MB System Card comes with these bonuses:
- A commericial copy of the Desktop Designer Application
- A commericial copy of the Eliza for C64 OS Application
- A copy of the Fart Machine Application
- A collection of CGFX animations, panoramas and matrix images
- A collection of PETSCII Bots
- Plus all the bonuses of the 64 MB system card
C64 OS is available for purchase as a physical product, and
Starts at just $64 CAD*
* $64 CAD is approximately $45 USD, for the Standard Bundle.
Not including shipping or applicable sales tax.

Testimonials

I have used C64 OS literally every day since I received it, even if it was just to turn on my C64 and see it load, and it brings a smile to my face that it exists every time! 😊
The app launcher itself has definitely proved to be something that makes it significantly easier for me to use my C64 for finding and running various applications in my day, where often my time at my desk is limited. Thank you again! Adam K0FFY — November 2022 — X (Twitter) DM

C64 OS is the perfect blend of modern OS concepts with sympathy for the classic Commodore 64! It has rekindled my interest in the design and implementation of computer operating systems. It's an absolute delight to use, and sometimes fools you into thinking you're working on a machine designed this millennium!
If you want to write software for your Commodore 64, C64 OS does almost all of the heavy lifting for you. Matt Stine — September 2023 — Discord DM
Choose your C64 OS bundle.
Standard Bundle (64 MB System Card)

The standard bundle comes with a 64 MB System Card. A complete copy of C64 OS is pre-installed and ready to be used with an SD2IEC. An installation archive and install tools are included which can be used to install C64 OS on other supported storage media. In addition, a CMD HD hard drive image (DHD) and an IDE64 hard drive image (HDD) is included each with a pre-installed copy of C64 OS, ready for use with VICE. You'll also get a professionally printed full-color 50-page User's Guide and two high quality vinyl C64 OS promo stickers.
The 64 MB System Card is enough to hold the capacity of hundreds of 1541 disk sides. You'll have room to use C64 OS, install future updates, and add new Applications and Utilities as they become available, and still have plenty of space to install your favorite games, store all your documents, and have access to media files like pictures and music.
The System Card comes pre-partitioned with a main partition for C64 OS and a second partition for disk images. This allows you to mount disk images and use C64 OS to access and manage their content all from a single SD2IEC storage device. The System Card also comes packed with over 150 graphics files, and a selection of the top rated SIDs from HVSC.
Please review the minimum hardware requirements before you purchase C64 OS. You can also consult the frequently asked questions for additional information about hardware requirements and compatibility.
What's in the bundle?

- 64 MB System Card with 2 partitions, space for documents, games and media
- 50-page full-color printed User's Guide
- Pre-installed copy of C64 OS v1.07 for use with SD2IEC
- Pre-installed CMD HD hard drive image for use in VICE
- Pre-installed IDE64 hard drive image for use in VICE
- An installation archive and install tools for other storage media
- A collection of C64 graphics files that can be viewed with Image Viewer
- A collection of popular HVSC SID tunes that have been relocated for use in C64 OS
- Two high-quality vinyl 2" by 1" C64 OS promotional stickers
- An OpCoders Inc. Business Card
Extended Bundle (64 MB System Card + Extras)

The extended bundle comes with a 64 MB System Card. A complete copy of C64 OS is pre-installed and ready to be used with an SD2IEC. An installation archive and install tools are included which can be used to install C64 OS on other supported storage media. In addition, a CMD HD hard drive image (DHD) and an IDE64 hard drive image (HDD) is included each with a pre-installed copy of C64 OS, ready for use with VICE. You'll also get a professionally printed full-color 50-page User's Guide and two high quality vinyl C64 OS promo stickers.
The extended bundle comes with everything included in the standard bundle, plus it includes commercial copies of Eliza for C64 OS and Desktop Designer. The extended bundle also comes with the install archive of Fart Machine and a collection CGFX and other media files.
Please review the minimum hardware requirements before you purchase C64 OS. You can also consult the frequently asked questions for additional information about hardware requirements and compatibility.
What's in the bundle?

- 64 MB System Card with 2 partitions, space for documents, games and media
- 50-page full-color printed User's Guide
- Pre-installed copy of C64 OS v1.07 for use with SD2IEC
- Pre-installed CMD HD hard drive image for use in VICE
- Pre-installed IDE64 hard drive image for use in VICE
- An installation archive and install tools for other storage media
- A collection of C64 graphics files that can be viewed with Image Viewer
- A collection of popular HVSC SID tunes that have been relocated for use in C64 OS
- Two high-quality vinyl 2" by 1" C64 OS promotional stickers
- An OpCoders Inc. Business Card
- Install archive of Eliza for C64 OS
- Install archive of Desktop Designer
- Install archive of Fart Machine
- A collection of CGFX animations, panoramas and matrix images
- A collection of PETSCII Bots
Watch C64 OS in Action
C64 OS Video Demonstrations
Curious to know more about what C64 OS can do? What it's like to use it? Watch these two video demonstrations recorded for Commodore User's Europe showing the state of C64 OS and some of its useful and powerful features.
The first presentation is from June 2021. It shows many features that were complete at that time, but many features in the final version 1.0 were not yet available.
The second presentation is from one year later, June 2022. The second presentation is much closer to the version 1.0 release and also includes a lengthy Q&A session at the end.
Presentation #4: November 2024 (63 minutes)
Connect with clicks: C64 OS goes online
Presentation #3: December 2023 (56 minutes)
Advanced new features in C64 OS
Presentation #1: June 2021 (23 minutes)
C64 OS makes a C64 feel fast and useful
Presentation #2: June 2022 (51 minutes)
C64 OS nearing v1.0 release
Checkout the complete online User's Guide, for a detailed discussion of many more features and capabilities of C64 OS.
C64 OS Reviews and Unboxings
Reviews are different from demos. In the demos above, C64 OS is presented on a tight schedule with a prepared set of talking points to move quickly and show off the latest key features and abilities.
In a review or an unboxing, the host may be trying out C64 OS for the very first time, and is not an experienced C64 OS user who knows all the tricks and shortcuts. Therefore, reviews are a sort of adventure, exploring novelty and discovering what might be found. Some things mentioned may be slightly inaccurate and the hardware upon which the review is being run may be slower or less powerful than other possible hardware combinations.
Retro Recipes C64 OS Review (40 minutes)
4.5 out of 5 chips review of C64 OS v1.0
Amy and Taylor unbox C64 OS (12 minutes)
An eager and fun first impressions of C64 OS v1.0
C64 OS Interviews
Listen to a meandering podcast interview about C64 OS and other miscellaneous C64 topics, at Scene World with:
- Joerg Droege
- AJ Heller, and
- Greg Nacu

Listen to a podcast interview about C64 OS, at New Game Old Flame with:
- Andy
- Diego, and
- Greg Nacu

Listen to a podcast interview about C64 OS, at The Hanselminutes Podcast with:
- Scott Hanselman, and
- Greg Nacu

C64 OS + Hardware Collections
New software, new hardware, all new capabilities.
A C64 fan's dream come true.
The following hardware collections are a sample from a myriad of possible combinations. They give a broad overview of the progression from the simplest and least expensive way to get more out of your C64 by running C64 OS, to the more advanced and modern collections that look fantastic and also offer the most powerful opportunities for C64 OS to take advantage of.
Barebones Collection
- A C64 Breadbin
- A Joystick
- An SD2IEC
- And C64 OS
The only new kit needed is an SD2IEC—these come in a multitude of form factors, some cost as little as $45 USD—and that's all you need to get into C64 OS.
Explorer Collection
- A C64 Breadbin
- A 1351 Mouse
- An SD2IEC
- And C64 OS
If you want to explore C64 OS further, the most obvious next step is to switch the joystick out for a mouse. If you can't find a 1351 there are many adapters for modern mice.
Hipster Collection
- A Commodore 64c
- A 1351 Mouse
- A Cableless SD2IEC
- And C64 OS
Step up to the sleeker C64c but keep the 1351 for that retro hipster feel. A cableless SD2IEC eliminates the serial cable for a tighter more modern look.
Serious Collection
- A Commodore 64c
- A 1351 Mouse
- The JiffyDOS KERNAL
- A Cableless SD2IEC
- And C64 OS
If you want to get serious about using your C64 with C64 OS, upgrading your KERNAL ROM to JiffyDOS is the first best step.
Modern Collection
- An Ultimate 64
- A PS/2 or USB Mouse with adapter
- The JiffyDOS KERNAL
- A Cableless SD2IEC
- And C64 OS
The Ultimate64 takes a JiffyDOS ROM image, offers an RTC and a 16MB REU. Pair it with a cableless SD2IEC and a USB mouse and MouSTer for a modern C64 OS experience.
Network Collection
- An Ultimate 64
- A PS/2 or USB Mouse with adapter
- The JiffyDOS KERNAL
- A Link232 WiFi Cartridge
- A Cableless SD2IEC
- And C64 OS
Take the final step by adding a highspeed serial port with built-in TCP/IP WiFi modem, and your C64 is ready to follow C64 OS as it marches into the future.
Guides and Documentation
Jump in quickly with the Getting Started Guide.
Explore many features in more detail with the User's Guide.
|
Getting Started Guide |
User's Guide |
Networking Guide |
Programmer's Guide |
New or returning to the Commodore 64?
Are you new to the Commodore 64 and want to dive in and explore this culture-shaping classic computer? Or are you a returning user who had a C64 in your youth, and you've got the itch to relive old memories and start building new ones?
The Commodore 64 is a simple and fun machine, but it's a bit quirky and philosophically different from modern computers. Rather than read through old books to bring yourself up to speed, start with this:
|
An Afterlife User's Guide to the C64 |
Useful Resources
What's New
Every time a new version of C64 OS is released the major new features, Applications and Utilities are presented on the "What's New!" page. If you're getting ready to update your system, or interested to know what an update will bring you, be sure to check out what's new.
Your Account
From your C64OS.com account you can update your name, email address and account password. You can review your purchase history from OpCoders Inc. You can find an invitation link to join the C64 OS Community Support Discord server.
From your account you can also subscribe to the C64 OS Network Proxy Services, manage your access credentials, and get important networking configuration information.
C64 OS Software Releases
Download new software to expand what C64 OS is capable of doing. This is the official place where C64 OS software releases are posted and can be found. Grouped in categories like entertainment, productivity, utilities and networking.
C64 OS System Updates
System software updates are available for download. Install them to update C64 OS to the next version. Each system update brings exciting new features, new low-level capabilities, and new bundled Apps and Utilities.
C64 OS on Real Hardware
Check out this growing gallery of user submitted photos of their C64 OS setup. It's so inspiring to see how other C64 OS users put their gear together. Submit a photo or two of your setup and they'll get added to an upcoming collage.
C64 OS Media Resources
Your place to download special C64 OS media resources, including official 3.5" floppy disk labels to create your own C64 OS System Disks on FD-2000 and FD-4000, branded 5.25" floppy disk sleeve templates, wallpapers for Mac/PC, and the special "Made for C64 OS" mark you can use on your websites that promote your C64-OS-specific Applications, Utilities, tools and programs.
Download C64 OS media resources ⇒
Last modified: May 22, 2025